Scanners find the problems. But prioritization, routing, remediation, and verification still land on your team manually. Blink's Agentic Security Operations Platform deploys dedicated AI agents across every stage of your vulnerability management lifecycle. Fully customizable around your policies and procedures. Not a black box.
Scanners produce thousands of findings. Prioritization is manual. Tickets get created and sit in a queue for weeks. Remediation depends on engineers who have other jobs. The backlog never shrinks.
Tenable, Qualys, Wiz, and Defender each report thousands of findings. Without business context, every CVE looks equally urgent. Nothing gets fixed first.
Security finds the issue. IT owns the fix. Cloud teams patch. DevOps deploys. Every step is a ticket, an email, a Slack message. The window widens.
Vulnerability data in one tool. Asset inventory in another. Patch history in CMDB. Nobody has the full picture and nobody can track what actually got fixed.
Critical vulnerabilities sit unpatched past SLA. When auditors ask, the answer is a spreadsheet. Evidence collection takes weeks instead of seconds.
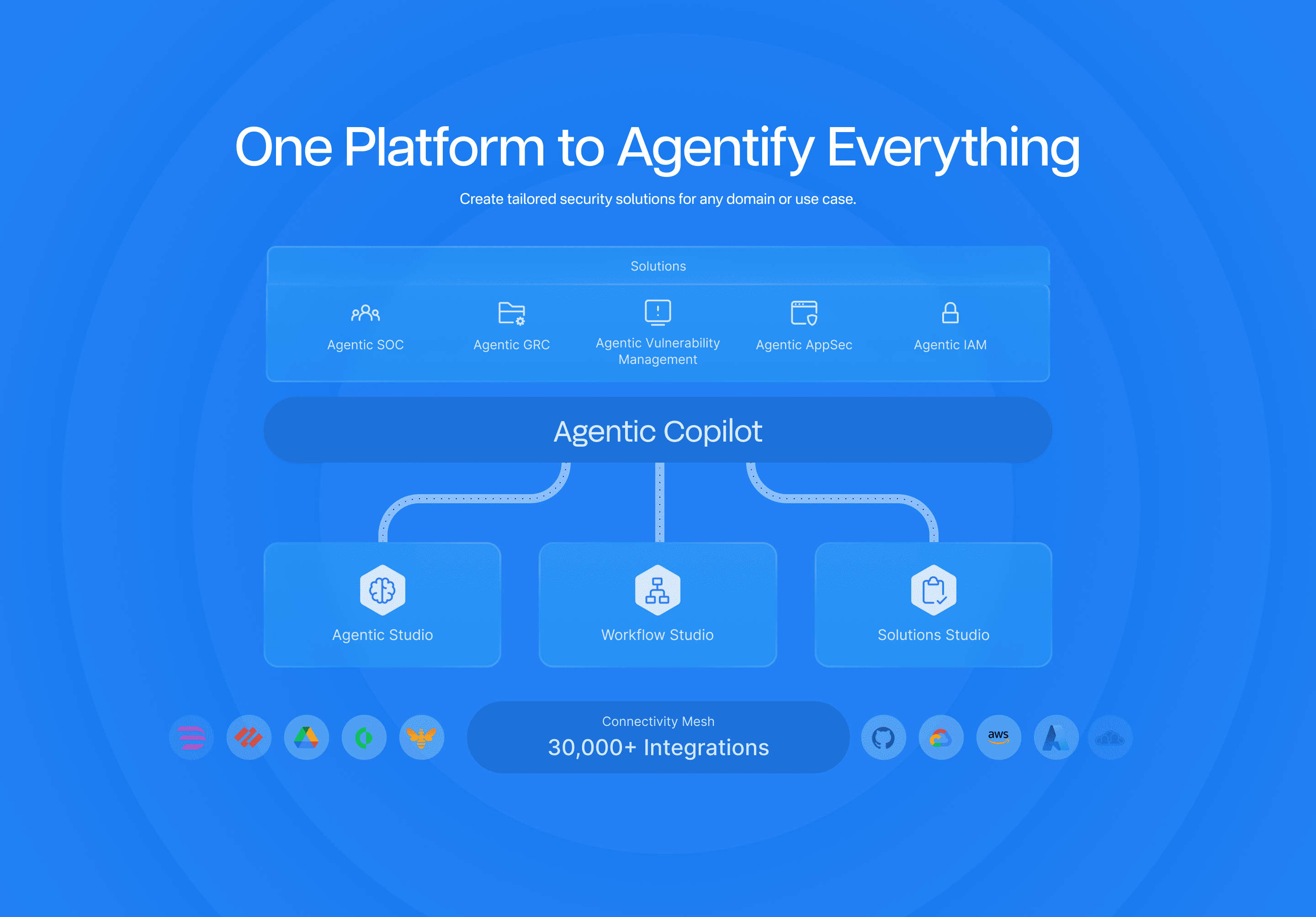
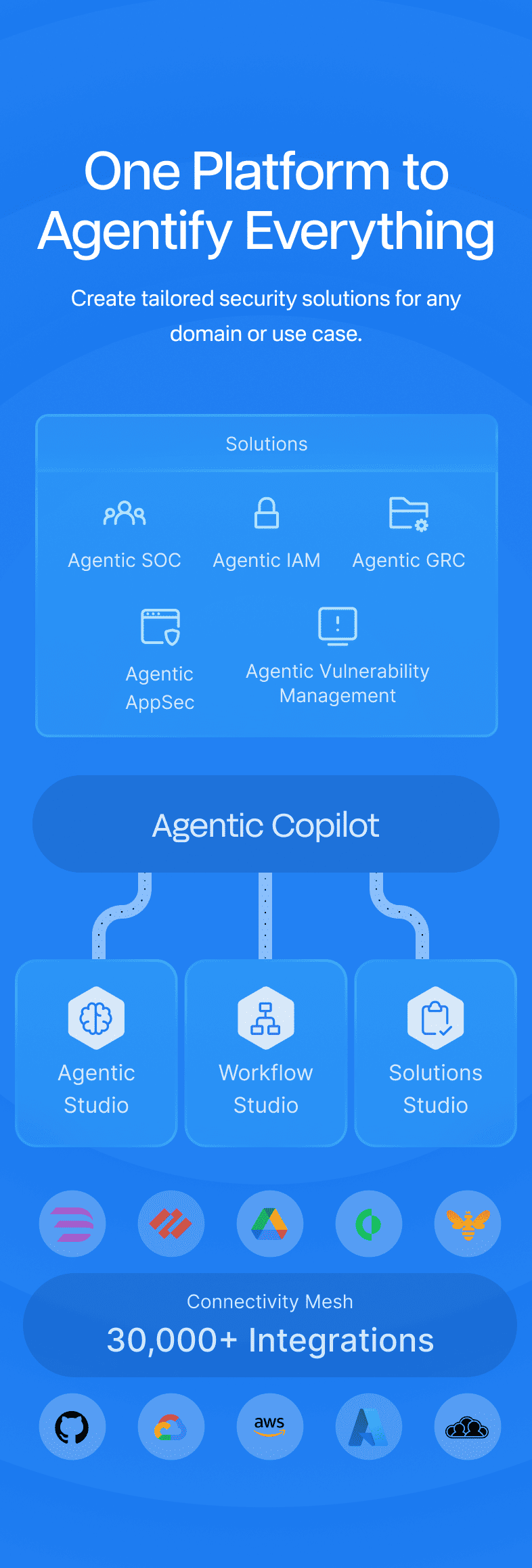
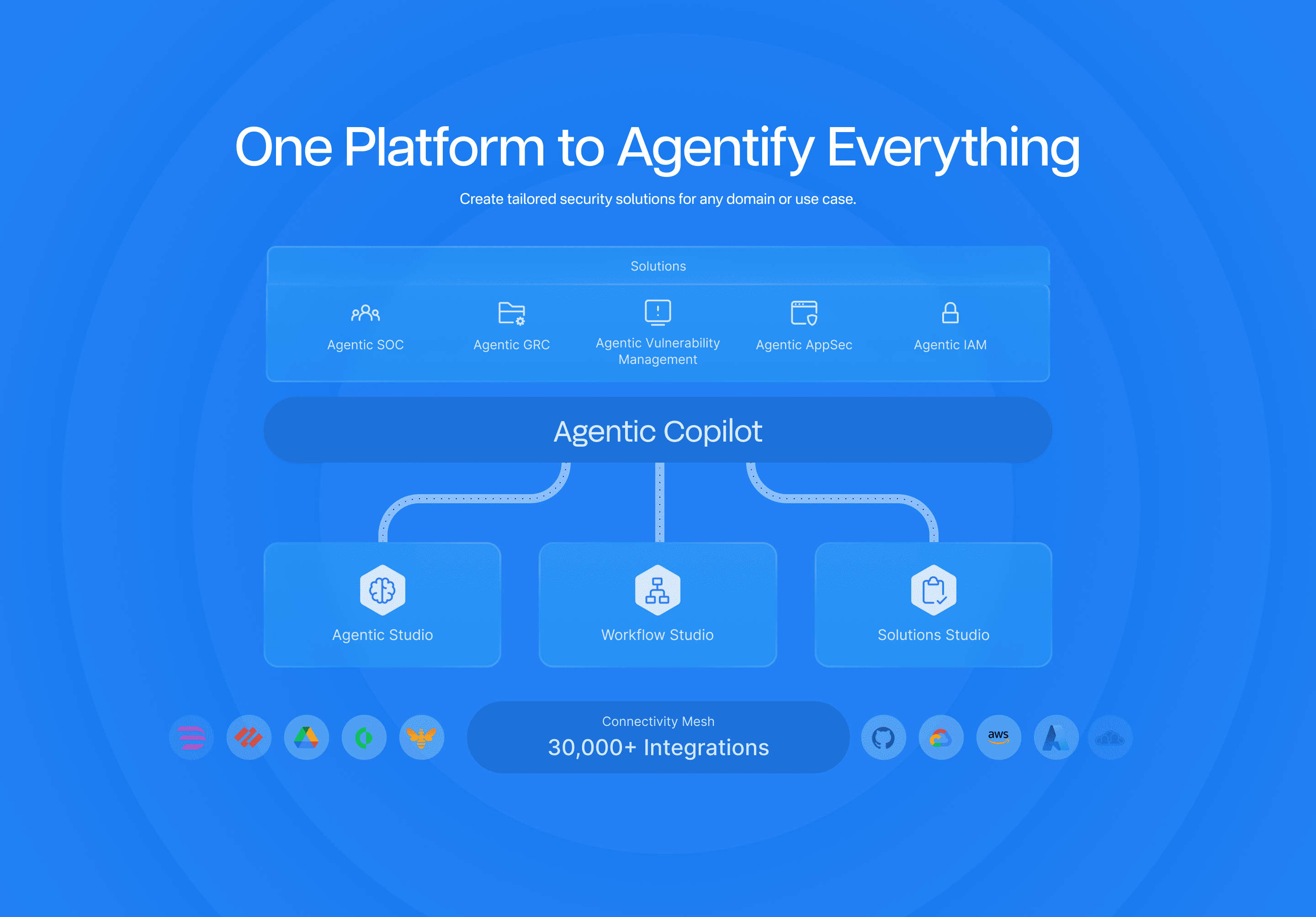
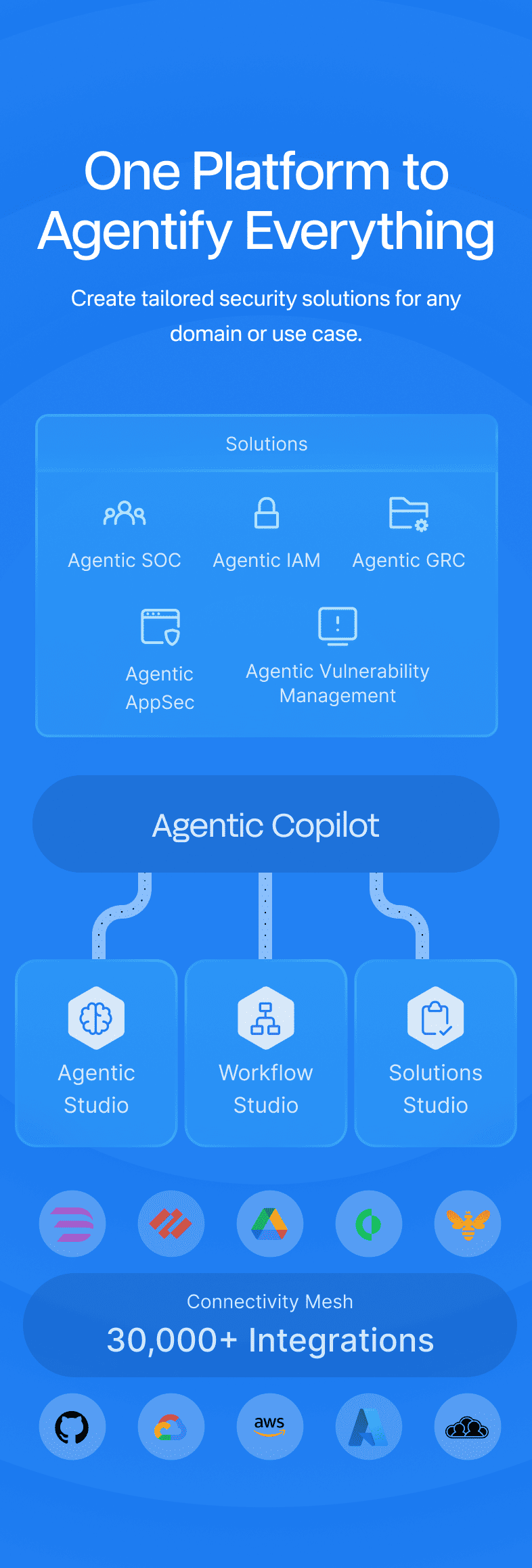
Vulnerability management follows the same operational loop as any security function: ingest findings, analyze what matters, decide what to fix first, then execute. The problem is that most VM programs run this loop manually, across disconnected tools, with humans bridging every gap. Blink agents operate across every phase of the SUDA loop so your VM pipeline runs continuously.
Agents ingest findings from every scanner in your environment: Tenable, Qualys, Wiz, Prisma, Defender, Rapid7. Findings are normalized, deduplicated, and fed into a unified case management layer. Every vulnerability tracked in one place from the moment it is discovered.
CVSS alone is not enough. Agents layer in EPSS exploitability scores, asset criticality from your CMDB, internet exposure, business unit context, and your organization's risk appetite.
Prioritization reflects your environment, not a generic severity number from a vendor.
Agents route findings to the right team, in the right format, with the right context. Routing follows your SLA policies, your org structure, your escalation paths. Critical findings get fast-tracked. Low-risk items get grouped and batched.
Everything aligned with how your company actually operates.
Agents orchestrate remediation across cloud, patch management, CMDB, and DevOps toolchains. After the fix is deployed, they trigger a re-scan to verify. Once confirmed, the case is closed with a full audit trail. The remediation process follows your company's change management and approval procedures, not a one-size-fits-all playbook.
Blink ships with pre-built VM agents you can deploy in minutes. Need to go deeper?
Build custom agent logic, deterministic workflows, or compliance dashboards
yourself — or bring in our Forward Deployed Engineers to build alongside you.
Other VM tools give you findings and stop — or give you remediation logic you can't modify. Blink ASOP is different. You choose how you engage.

Automated remediation is powerful. Unconstrained automation is dangerous. Every Blink agent operates within defined guardrails. You control what it can touch, what it can change, and when it needs to ask.
"Blink's no-code automations remove bottlenecks and communication issues, by enabling any engineer to share 1-click apps and streamline otherwise complicated processes."
CISO,
Rapyd
Most things I need exist, off the shelf. The few things not already available magically appear after a short chat with the Blink team. The documentation for setting up integrations is seriously world class, I've never had a smoother integration process.
Head of Platform Engineering,
KOHO Financial
Today it's faster for us to create new cloud workflows. We don't need to learn all the authentication steps and syntax of each product anymore.
SecOps Team Leader,
ControlUp
Connect your scanners, define your prioritization logic, and deploy a
fully operational VM pipeline. BlinkOps Forward Deployed Engineers
work alongside your team the whole way.
Connect your scanners and asset inventory. All findings flow into unified case management with no manual export.
Configure agent logic based on asset criticality, business units, SLA policies, and your organization's risk tolerance.
Agents go live across ingestion, prioritization, routing, and remediation. Your team tracks cases, not spreadsheets.
Add agents for specific vulnerability classes, asset groups, and remediation teams. Tune prioritization and routing as your environment evolves.